All companies that have been victims of a cyberattack will confirm that when it comes to computer security, it is better to favor prevention than remediation.
To do so, risk analysis is essential in your cybersecurity strategy. Among other things, it will allow you to take stock of the threats hanging over your organization, the vulnerabilities of your systems, and the importance of the asset that could be damaged.
Let’s see together through this article how risk analysis allows you to anticipate risks to better avoid them!
What is a risk
In the field of cybersecurity, the “risk” consists of 3 main axes:
- An asset is a resource, process, product or system that has some value to an organization and needs to be protected
- A threat is any natural or man-made circumstance that could harm an asset
- A vulnerability is a gap in the protection of an asset that allows a threat to materialize
In cybersecurity, we speak of risk when a threat exploits a vulnerability of an IT asset.
Organizational risk is a threat that materializes due to a vulnerability in managing an organization’s assets.
Here are some concrete examples of these 3 main areas:

What is a risk analysis
Risk analysis is an exercise that identifies and studies risks. It makes it possible to propose mitigation or remediation actions.
Thus, the risk analysis is divided into 7 main steps:
- Step 1: Identify scope and context
- Step 2: Inventory the assets and identify their criticality
- Step 3: Identify vulnerabilities and threats
- Step 4: Analyze the risks and determine their impacts
- Step 5: Define the tolerance threshold (risk appetite)
- Step 6: Deal with risks that exceed the tolerance threshold
- Step 7: Monitor the evolution of risks
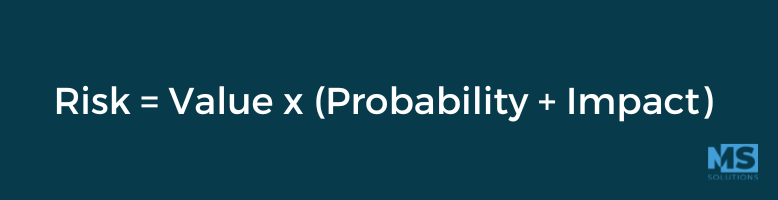
Once the analysis is completed, it is a question of dealing with the identified risks. All risks are not equal, we will then evaluate and compare the risks in order to assess both their impact and their probability. To do this, we rely on the following method, which is based on the fact that a risk is calculated according to three variables:
- The value of the asset
- The likelihood of the threat occurring
- The impact of the threat
Once these 3 variables have been defined, here is the formula to use:
There are various methods to analyze and prioritize the risks of an organization. It is important to choose one that you are comfortable with.
What are the benefits
A risk analysis has many benefits for the organization. Among other things, it makes it possible to become aware of the important assets of the organization. On the other hand, the identification of threats, vulnerabilities, impacts and their probability provides an overview of the risks hanging over the organization.
The risk analysis will also make it possible to harmonize the protection efforts with the objectives of the company. It will help to make decisions on the protections to deploy. This allows you to have a risk treatment plan.
What are the main areas of risk
Ignoring the risk analysis exercise amounts to exposing oneself to many areas of risk. We can never repeat it enough, a cyberattack can cost your organization dearly both financially and in terms of your public image.
Brand image, loss of business opportunities, financial loss, business interruption, non-compliance, data compromise, are all risks to which you expose yourself when you do not take your cybersecurity seriously.
In short
As we have seen through this article, risk analysis is a relevant exercise for any company concerned about its sustainability. The risk analysis makes it possible to establish both a balance sheet of the organization’s assets while having a precise and lucid vision of the risks that are on it.
Betting on risk analysis therefore allows you to be proactive in the face of the risks that threaten you, because anticipation is the key to an optimal cybersecurity strategy.
Do you want to improve your security posture and would you like to be accompanied? Do not hesitate to contact our team for more information. Our experts will be able to support you in your process towards optimal cybersecurity.