A phishing scam involves tricking the recipient into responding to a request, whether it’s to click on a link, install an attachment, or transfer money. Phishing messages are sent from what appears to be a trusted source and individual recipients tend to ignore subtle, but clear signs that something is wrong. Let’s take a look at the different types of phishing so that you can identify them and thus protect yourself from these types of attacks.
Increasingly connected, our email inboxes and our social media channels are full of phishing attempts. Who has never received a suspicious link via Facebook, or an email from a well-known firm claiming that you have been drawn in a lottery in which you did not participate… We grant you that, some are more credible than others both in substance and in form!
Hackers are full of tricks to be able to trap us and escape our vigilance. We have listed these attacks in 3 main families: mass phishing, spear phishing, and whaling.
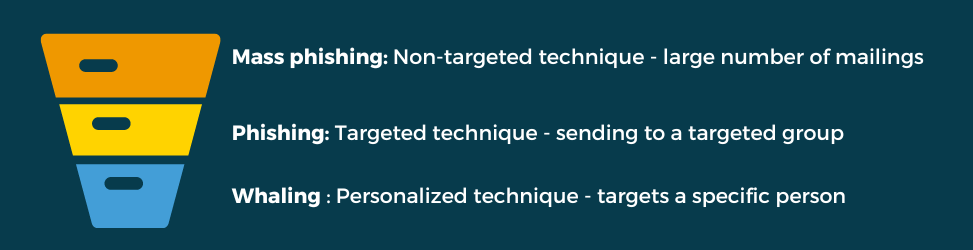
Mass Phishing
Mass phishing is not targeted. The hacker will send his attack to a large number of people to increase the chances of someone falling into his trap. He does not need to inquire about his victims, and will, for example, pretend to be a known entity.
For example, an email pretending to be from Netflix or Amazon asking you to change your password.
Phishing
Spear-phishing is a more targeted technique. The hacker will target a group of victims. Since the technique is very vicious, the hacker often impersonates the very entity he wants to access.
For example, an email from your company that contains a malicious attachment.
Whaling
Whaling (big fish) is a specific and very targeted type of phishing. Computer hackers will target influential or well-known personalities (executives, politicians, etc.).
This technique aims to deceive the recipient by using social engineering to collect important information about the company.
For example, an email that redirects to a website specially designed for the attack and very personalized.
MS Solutions advice: Even if the e-mail seems realistic to you, or comes from a known e-mail, do not hesitate to verify the information, by calling the sender for example, to ask him to confirm that he is indeed the originator of the e-mail by question. This reflex will allow you to avoid an error that can be very costly.
In short …
As we have seen, each hacker has his technique to get you hooked! Knowledge of these techniques remains your best weapon to enable you to identify them when you are confronted with them.
If you want to deepen your team’s knowledge of cybersecurity, don’t hesitate to call on our experts who can advise you on the latest methods in terms of phishing awareness.